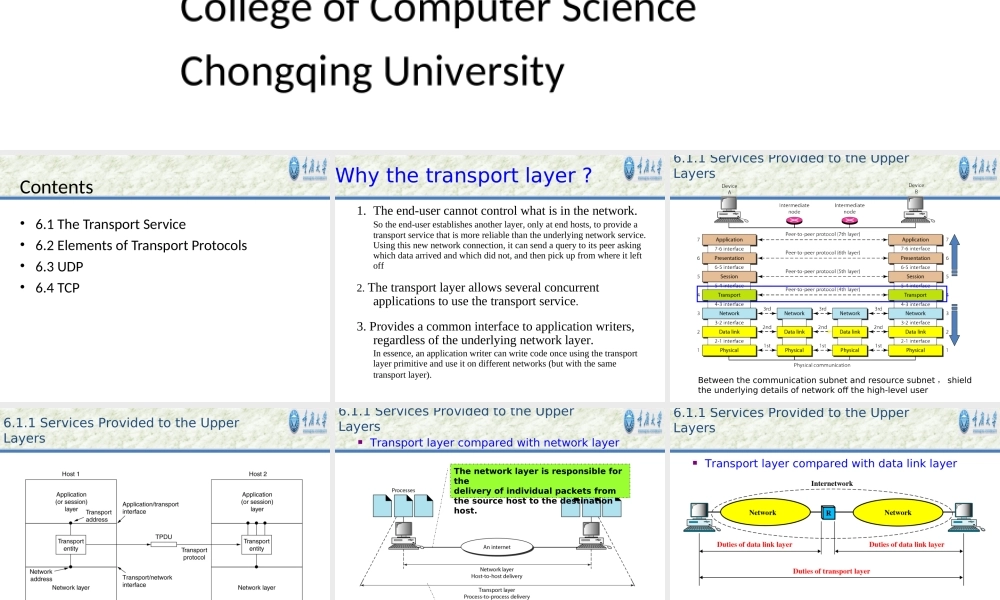
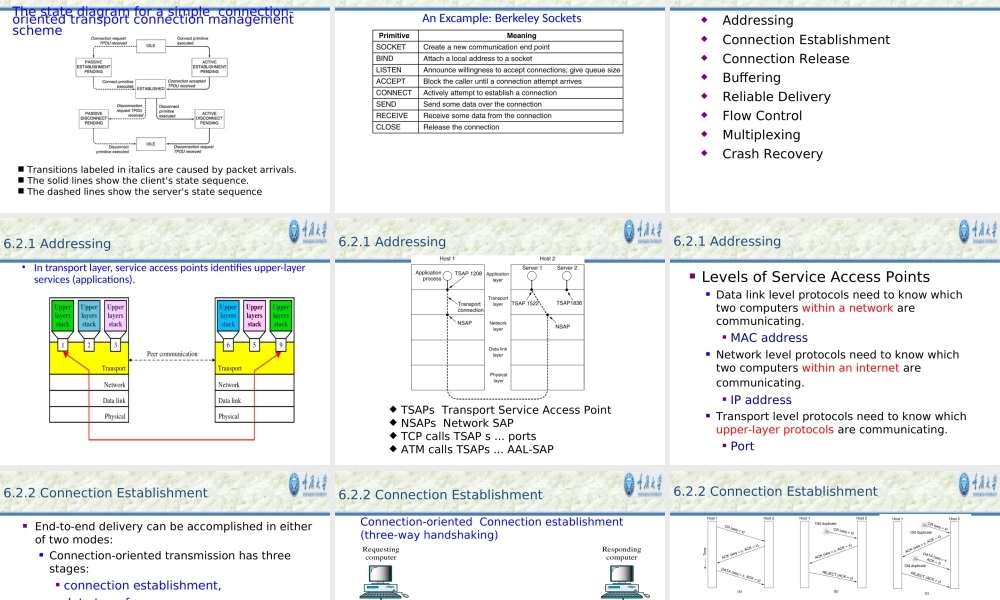
Chapter6TheTransportLayerCollegeofComputerScienceChongqingUniversityContents•6.1TheTransportService•6.2ElementsofTransportProtocols•6.3UDP•6.4TCP1.Theend-usercannotcontrolwhatisinthenetwork.Sotheend-userestablishesanotherlayer,onlyatendhosts,toprovideatransportservicethatismorereliablethantheunderlyingnetworkservice.Usingthisnewnetworkconnection,itcansendaquerytoitspeeraskingwhichdataarrivedandwhichdidnot,andthenpickupfromwhereitleftoff2.Thetransportlayerallowsseveralconcurrentapplicationstousethetransportservice.3.Providesacommoninterfacetoapplicationwriters,regardlessoftheunderlyingnetworklayer.Inessence,anapplicationwritercanwritecodeonceusingthetransportlayerprimitiveanduseitondifferentnetworks(butwiththesametransportlayer).Whythetransportlayer?Betweenthecommunicationsubnetandresourcesubnet,shieldtheunderlyingdetailsofnetworkoffthehigh-leveluser6.1.1ServicesProvidedtotheUpperLayers6.1.1ServicesProvidedtotheUpperLayersThenetworklayerisresponsibleforthedeliveryofindividualpacketsfromthesourcehosttothedestinationhost.Thetransportlayerisresponsibleforthedeliveryofamessagefromoneprocesstoanother6.1.1ServicesProvidedtotheUpperLayersTransportlayercomparedwithnetworklayerTransportlayercomparedwithdatalinklayer6.1.1ServicesProvidedtotheUpperLayersSimilaritiesBothhavetodealwitherrorcontrol,sequencing,andflowcontrol,amongotherissuesdifferences1.Generallydirectedconnected2.PointtoPointbased3.3.connectionestablishmentisconnectionestablishmentissimplesimple4.storagemanagementissimple,Out-buffers/in-buffers1.Connectedviasubnet2.explicitaddressingofdestinationsisrequired3.3.connectionestablishmentismoreconnectionestablishmentismorecomplicatedcomplicated4.Connectionbasedin/out-buffermangement6.1.1ServicesProvidedtotheUpperLayersTransportlayercomparedwithdatalinklayerTransportlayerconcept6.1.1ServicesProvidedtotheUpperLayersThenestingofTPDUs,packets,andframes6.1.1ServicesProvidedtotheUpperLayersEnd(normallyprocessesintheapplicationlayer)toenddeliveryReliable...