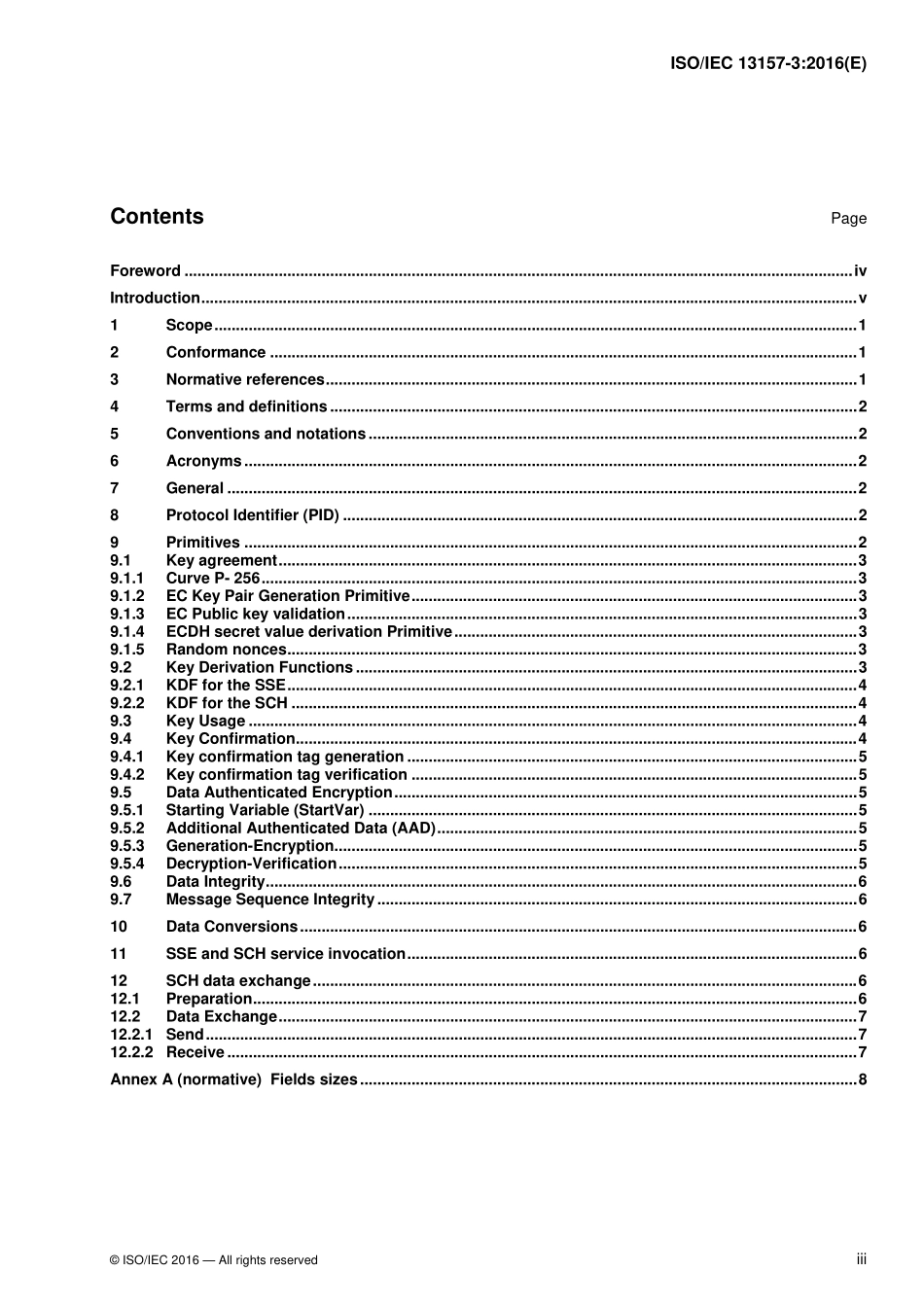
Informationtechnology—Telecommunicationsandinformationexchangebetweensystems—NFCSecurity—Part3:NFC-SECcryptographystandardusingECDH-256andAES-GCMTechnologiesdel’information—Téléinformatique—SécuritéNFC—Partie3:NormedecryptographieNFC-SECutilisantECDH-256etAES-GCMINTERNATIONALSTANDARDISO/IEC13157-3ReferencenumberISO/IEC13157-3:2016(E)Firstedition2016-04-01©ISO/IEC2016ii©ISO/IEC2016–AllrightsreservedCOPYRIGHTPROTECTEDDOCUMENT©ISO/IEC2016,PublishedinSwitzerlandAllrightsreserved.Unlessotherwisespecified,nopartofthispublicationmaybereproducedorutilizedotherwiseinanyformorbyanymeans,electronicormechanical,includingphotocopying,orpostingontheinternetoranintranet,withoutpriorwrittenpermission.PermissioncanberequestedfromeitherISOattheaddressbeloworISO’smemberbodyinthecountryoftherequester.ISOcopyrightofficeCh.deBlandonnet8•CP401CH-1214Vernier,Geneva,SwitzerlandTel.+41227490111Fax+41227490947copyright@iso.orgwww.iso.orgISO/IEC13157-3:2016(E)ISO/IEC13157-3:2016(E)©ISO/IEC2016—AllrightsreservediiiContentsPageForeword............................................................................................................................................................ivIntroduction.........................................................................................................................................................v1Scope......................................................................................................................................................12Conformance.........................................................................................................................................13Normativereferences............................................................................................................................14Termsanddefinitions...........................................................................................................................25Conventionsandnotations................